Hi,
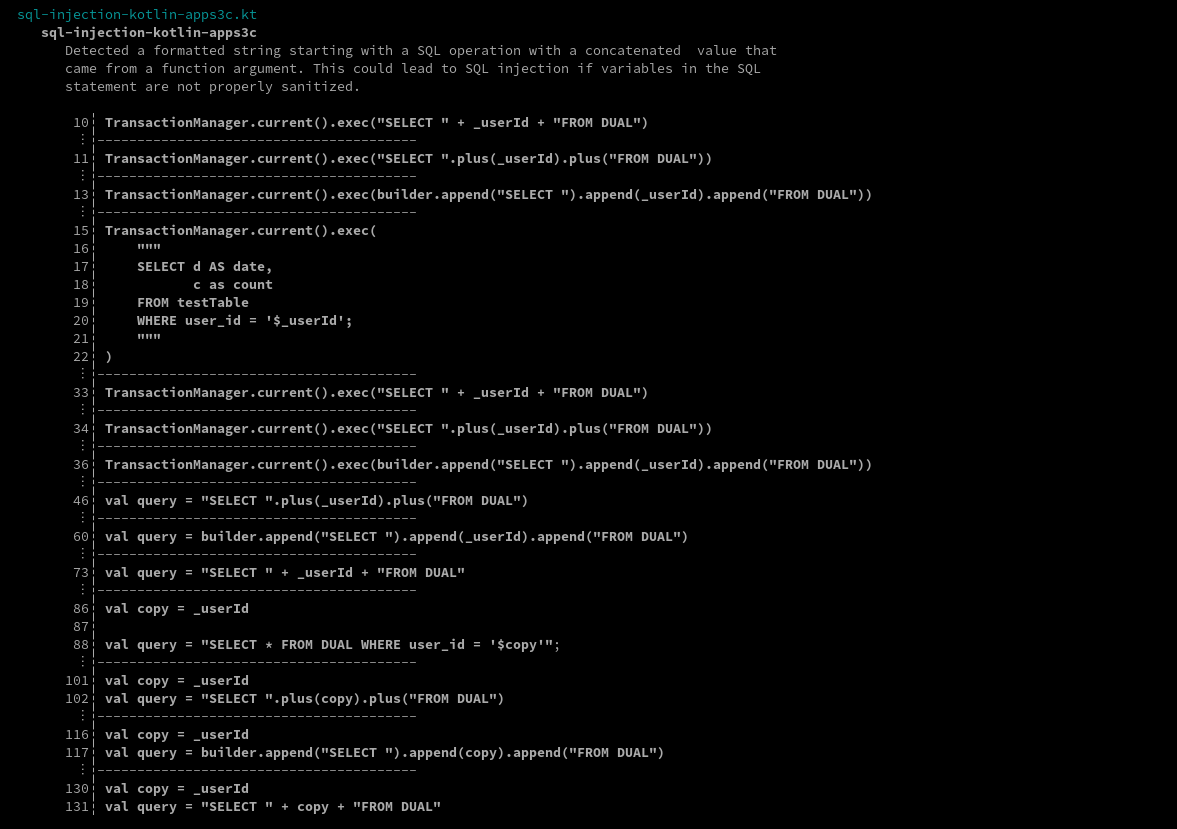
I recently had the chance to assess the security of many applications with a back-end written in the Kotlin language. Unfortunately, at the moment Semgrep‘s support for the Kotlin is still in “Beta” and there are not many public rules for this language. So, I decided to write a bunch of them on my own, mainly to look for potential SQL Injections. These rules were written with limited time, they are non-exhaustive, and can definitely be optimized. However, they are field-tested and have proven to do their job quite well.
Meanwhile, I also wrote a couple of rules related to Android mobile application’s client code, to quickly identify WebView functionalities in order to inspect their security configurations (for more info, see Android Platform APIs page of OWASP Mobile Testing Guide), both for Java and Kotlin.
These rules can be found in my Semgrep rules repository on GitHub: https://github.com/federicodotta/semgrep-rules
If you’re interested in Semgrep and static analysis, you should also check out our Semgrep C/C++ and PHP rulesets for vulnerability research.
Cheers!